使用Win32DiskImager做安装kali启动U盘后的那些事儿 Linux
如题,前几天不是kali风骚的流产了么。。。他们的新儿子kali2.0,我就试试感觉咋样,于是呢,就需要使用Win32DiskImager来做kali的安装启动U盘啊,一切顺利。。。只是在安装完之后,我切换到win10时候,插入U盘发现U盘容量有问题。。。
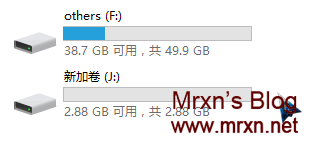
原本是8G的U盘,咋变这么小呢。。。开始尝试使用系统格式化工具-格式化,但是问题出现了。。。还是这么大、、、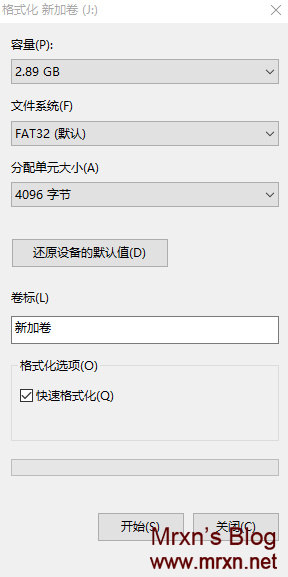
FormatTool..是个很不错的软件,但是你的自己记住你的U盘的盘符 g h j 等等。。。我的是J .把强制格式化复选框选上之后,确定,稍作等待。就OK了: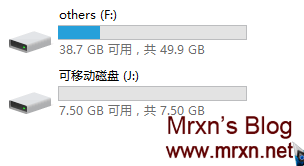
容量就恢复了。。。goodsoft!对了软件下载地址:http://pan.baidu.com/s/1o6mW0Ls 方便需要的童鞋下载。
Kali套件之nikto扫描网站漏洞应用小计 Linux
nikto帮助文档
帮助文档比较复杂,这里就使用最简单的几种方法:
root@kali:~# nikto -H
Options:
-ask+ Whether to ask about submitting updates
yes Ask about each (default)
no Don't ask, don't send
auto Don't ask, just send
-Cgidirs+ Scan these CGI dirs: "none", "all", or values like "/cgi/ /cgi-a/"
-config+ Use this config file
-Display+ Turn on/off display outputs:
1 Show redirects
2 Show cookies received
3 Show all 200/OK responses
4 Show URLs which require authentication
D Debug output
E Display all HTTP errors
P Print progress to STDOUT
S Scrub output of IPs and hostnames
V Verbose output
-dbcheck Check database and other key files for syntax errors
-evasion+ Encoding technique:
1 Random URI encoding (non-UTF8)
2 Directory self-reference (/./)
3 Premature URL ending
4 Prepend long random string
5 Fake parameter
6 TAB as request spacer
7 Change the case of the URL
8 Use Windows directory separator (\)
A Use a carriage return (0x0d) as a request spacer
B Use binary value 0x0b as a request spacer
-Format+ Save file (-o) format:
csv Comma-separated-value
htm HTML Format
msf+ Log to Metasploit
nbe Nessus NBE format
txt Plain text
xml XML Format
(if not specified the format will be taken from the file extension passed to -output)
-Help Extended help information
-host+ Target host
-IgnoreCode Ignore Codes--treat as negative responses
-id+ Host authentication to use, format is id:pass or id:pass:realm
-key+ Client certificate key file
-list-plugins List all available plugins, perform no testing
-maxtime+ Maximum testing time per host
-mutate+ Guess additional file names:
1 Test all files with all root directories
2 Guess for password file names
3 Enumerate user names via Apache (/~user type requests)
4 Enumerate user names via cgiwrap (/cgi-bin/cgiwrap/~user type requests)
5 Attempt to brute force sub-domain names, assume that the host name is the parent domain
6 Attempt to guess directory names from the supplied dictionary file
-mutate-options Provide information for mutates
-nointeractive Disables interactive features
-nolookup Disables DNS lookups
-nossl Disables the use of SSL
-no404 Disables nikto attempting to guess a 404 page
-output+ Write output to this file ('.' for auto-name)
-Pause+ Pause between tests (seconds, integer or float)
-Plugins+ List of plugins to run (default: ALL)
-port+ Port to use (default 80)
-RSAcert+ Client certificate file
-root+ Prepend root value to all requests, format is /directory
-Save Save positive responses to this directory ('.' for auto-name)
-ssl Force ssl mode on port
-Tuning+ Scan tuning:
1 Interesting File / Seen in logs
2 Misconfiguration / Default File
3 Information Disclosure
4 Injection (XSS/Script/HTML)
5 Remote File Retrieval - Inside Web Root
6 Denial of Service
7 Remote File Retrieval - Server Wide
8 Command Execution / Remote Shell
9 SQL Injection
0 File Upload
a Authentication Bypass
b Software Identification
c Remote Source Inclusion
x Reverse Tuning Options (i.e., include all except specified)
-timeout+ Timeout for requests (default 10 seconds)
-Userdbs Load only user databases, not the standard databases
all Disable standard dbs and load only user dbs
tests Disable only db_tests and load udb_tests
-until Run until the specified time or duration
-update Update databases and plugins from CIRT.net
-useproxy Use the proxy defined in nikto.conf
-Version Print plugin and database versions
-vhost+ Virtual host (for Host header)
+ requires a value
nikto使用示例
使用前需要更新nikto,输入命令:
|
nikto -update |
但有时候会出现网路问题,作者这里这样处理的,如下,不知道对不对。
|
root@kali:~# nikto -update |
|
|
+ Retrieving 'db_tests' |
|
我没有更新Kali系统,所以显示的不是最新版的nikto.
|
+ ERROR: Unable to get CIRT.net/nikto/UPDATES/2.1.5/db_tests |
首先查找文件【 db_tests 】:
|
root@kali:~# cd / |
|
|
root@kali:/# find . -name "db_tests" |
|
|
./usr/share/webshag/database/nikto/db_tests |
|
|
./var/lib/nikto/databases/db_tests |
|
然后删掉文件,重新更新,就可以了:
|
root@kali:/# cd /var/lib/nikto/databases/ |
|
|
root@kali:/var/lib/nikto/databases# rm db_tests |
|
|
root@kali:/var/lib/nikto/databases# nikto -update |
|
|
+ Retrieving 'db_tests' |
|
|
+ CIRT.net message: Please submit Nikto bugs to http://trac2.assembla.com/Nikto_2/report/2 |
如果还是不行,就手动下载:
|
root@kali:/var/lib/nikto/databases# wget CIRT.net/nikto/UPDATES/2.1.5/db_tests |
更新好之后就可以扫描了:
|
root@kali:/var/lib/nikto/databases# nikto -host http://192.168.168.109/DVWA-1.0.8 |
|
|
- Nikto v2.1.5 |
|
|
--------------------------------------------------------------------------- |
|
|
+ Target IP: 192.168.168.109 |
|
|
+ Target Hostname: 192.168.168.109 |
|
|
+ Target Port: 80 |
|
|
+ Start Time: 2015-04-30 20:08:40 (GMT8) |
|
|
--------------------------------------------------------------------------- |
|
|
+ Server: Apache/2.4.9 (Unix) OpenSSL/1.0.1g PHP/5.5.11 mod_perl/2.0.8-dev Perl/v5.16.3 |
|
|
+ Retrieved x-powered-by header: PHP/5.5.11 |
|
|
+ The anti-clickjacking X-Frame-Options header is not present. |
|
|
+ Cookie PHPSESSID created without the httponly flag |
|
|
+ Cookie security created without the httponly flag |
|
|
+ Root page / redirects to: login.php |
|
|
+ No CGI Directories found (use '-C all' to force check all possible dirs) |
|
+ Server leaks inodes via ETags, header found with file /DVWA-1.0.8/robots.txt, fields: 0x1a 0x4dba8594c3d80 |
|
+ File/dir '/' in robots.txt returned a non-forbidden or redirect HTTP code (302) |
|
|
+ "robots.txt" contains 1 entry which should be manually viewed. |
|
|
+ Allowed HTTP Methods: POST, OPTIONS, GET, HEAD, TRACE |
|
|
+ OSVDB-877: HTTP TRACE method is active, suggesting the host is vulnerable to XST |
|
|
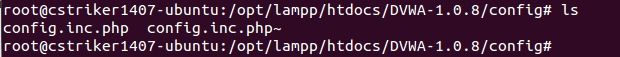
+ OSVDB-3268: /DVWA-1.0.8/config/: Directory indexing found. |
|
|
+ /DVWA-1.0.8/config/: Configuration information may be available remotely. |
|
|
+ OSVDB-3268: /DVWA-1.0.8/docs/: Directory indexing found. |
|
|
+ /DVWA-1.0.8/login.php: Admin login page/section found. |
|
|
+ 6545 items checked: 0 error(s) and 13 item(s) reported on remote host |
|
+ End Time: 2015-04-30 20:09:03 (GMT8) (23 seconds) |
|
--------------------------------------------------------------------------- |
|
|
+ 1 host(s) tested |
|
漏洞使用
877漏洞:
|
root@kali:/var/lib/nikto/databases# telnet 192.168.168.109 80 |
|
|
Trying 192.168.168.109... |
|
|
Connected to 192.168.168.109. |
|
|
Escape character is '^]'. |
|
|
|
|
|
get index.html |
|
|
|
|
|
。。。。。。 |
|
|
。。。。。。 |
|
|
<a href="/">localhost</a><br /> |
|
|
<span>Apache/2.4.9 (Unix) OpenSSL/1.0.1g PHP/5.5.11 mod_perl/2.0.8-dev Perl/v5.16.3</span> |
|
|
</address> |
|
|
</body> |
|
</html> |
|
|
|
|
Connection closed by foreign host. |
|
服务器的配置信息暴露了~~
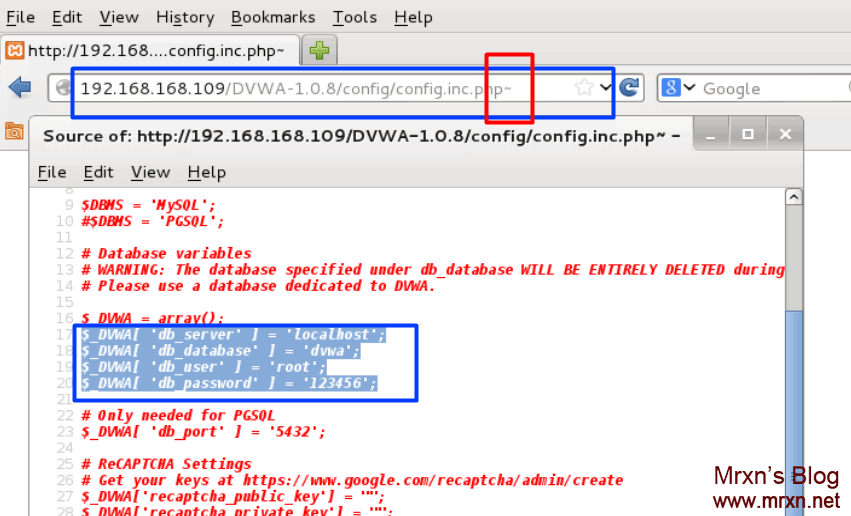
3268漏洞:
查看网页:
参看服务器端,果然有这个文件。
Kali折腾日记,解决不全屏、不能拖拽、复制的毛病之安装vmtools Linux
估计看着标题会有人会吐槽,你会就别说了!嘿嘿,下面开始:
0x1:
首先打开虚拟机上的Kali,然后在虚拟状态栏(最上面那一排)---->虚拟机------>安装vmware tools (然后Kali会出弹出一个文件夹)。
0x2:
打开终端,输入以下命令:
cd /media/cdrom0/ # 进入/media/cdrom0/
ls # 看下有哪些压缩文件
//注意:把VMwareTools*.tar.gz拷贝至/tmp/文件夹下面,然后执行下面命令即可 (VMwareTools*.tar.gz这个名字可能不一样哈)
cp VMwareTools*.tar.gz /tmp # *.tar.gz根据自己的版本拷贝至“文件系统”的tmp文件下
cd /tmp # 进入tmp文件夹
ls # 查看文件
tar -zxvf VMwareTools*.tar.gz # 解压VMWareTools压缩包
cd vmware-tools-distrib/ # 进入文件夹
./vmware-install.pl # 安装
根据提示有个地方需要选择“no”“yes”,它有提示的。
可以单条输入,也可以全部输入。
cd /media/cdrom0/
ls
cp VMwareTools*.tar.gz /tmp
cd /tmp
ls
tar -zxvf VMwareTools*.tar.gz
cd vmware-tools-distrib/
./vmware-install.pl
安装完成之后即可重启系统,reboot,然后可以尽情的在虚拟机和主机之间复制文件了!
如果做完以上步骤还是不能够使用,请往下看:
0X3:
//下面的解决办法是google出来的,在vm9上安装成功,支持拉伸屏幕、拖拽、复制粘贴。
8 ^4 ]+ |, p2 ?+ A/ V% k
1. 添加源:
deb http://debian.uchicago.edu/debian/ squeeze main contrib: B9 _- U! A# W5 H9 a
deb-src http://debian.uchicago.edu/debian/ squeeze main contrib
2.
#apt-get update
#apt-get install open-vm-tools open-vm-source
注:如果apt-get出错,可以试试下面两条语句#module-assistant auto-install open-vm -i+ d2 S( |+ i0 ]
#mount -t vmhgfs .host:/ /mnt/hgfs8 O2 W7 |! f* f/ a! n0 Z7 x# k
& x. w: ]) t5 w. U7 F
3.#apt-get install open-vm-toolbox& B) o' ?: P$ T i" u/ n. K# F
5 f' Q1 F1 I% A2 J$ q8 O
然后,没有然后了!!!/
By——Mrxn收集测试整理,转载请注明出处。